Have you ever heard of the concept of “Quantum computers”?
Quantum computers are a new kind of computing technology that uses the principles of quantum mechanics to process information differently from classical computers, which can perform specific tasks much faster, like breaking encryption or simulating complex systems. Over the past years, significant research has focused on quantum computers, which harness quantum mechanical principles to tackle complex mathematical problems beyond classical computers’ capabilities. If large-scale quantum computers were to become a reality, they could potentially undermine the security of current public-key encryption systems, posing a severe threat to the privacy and integrity of digital communications across the internet and other platforms.
Nonetheless, as the saying goes, “modern problems require modern solutions.” NIST initiated its quantum-resistant algorithm development endeavor in 2016 by inviting cryptographic experts worldwide to propose algorithms for the NIST Post-Quantum Cryptography Standardization Project. The objective of post-quantum cryptography, also known as quantum-resistant cryptography, is to create cryptographic systems that remain secure against both quantum and classical computers while being compatible with current communication protocols and networks.
In this blog today, let’s explore the groundbreaking significance of NIST’s latest milestone and its profound implications for the future of digital security.
NIST’s Draft Standards for Post-Quantum Cryptography
Post-quantum cryptography (PQC) has reached another significant milestone. On August 24, 2023, the U.S. National Institute of Standards and Technology (NIST) unveiled the initial draft standards for Post-quantum cryptography. Michela Menting from ABI Research elaborates on the announced standards and their impact on our evolving tech landscape.
NIST has chosen three of the four candidate algorithms it introduced in July 2023 and crafted draft standards that are now available for public review and commentary. These standards include:
- FIPS 203, Module-Lattice-Based Key-Encapsulation Mechanism Standard, founded on CRYSTALS-Dilithium.
- FIPS 204, Module-Lattice-Based Digital Signature Standard, rooted in CRYSTALS-KYBER.
- FIPS 205 is a stateless hash-based digital signature standard based on SPHINCS+.
The deadline for submitting comments is November 22, 2023. NIST is currently developing a Federal Information Processing Standards (FIPS) using the fourth candidate algorithm, FALCON, a digital signature algorithm.
This announcement is pivotal to incorporating quantum-resistant security measures into modern information and communication infrastructure. Since NIST initiated the standardization process in 2017, there have been significant advancements in quantum computing, prompting governments to establish policies on this matter and the industry sector to focus on risk assessment and mitigation.
Are We Quantum-ready?
From a commercial standpoint, the world is currently ill-prepared for the advent of quantum computing. It is anticipated that quantum computers capable of launching attacks won’t emerge before 2030, and the transition to post-quantum security measures will likely take a decade or more. Consequently, the efforts to standardize these security measures, especially those led by NIST, play a pivotal role in spurring industry adoption. However, NIST is just the initial step in this transitional process.
The participation of other Standards Development Organizations (SDOs), such as the Internet Engineering Task Force (IETF), ETSI (European Telecommunications Standards Institute), and the ITU (International Telecommunication Union), is equally crucial in the formulation of protocols and recommended practices for diverse applications.
Concurrently, within specific industry groups and consortia, development initiatives will proceed in tandem with open-source movements. These endeavors will essentially build upon the standards and recommendations established by SDOs, optimizing their specifications and reference architectures. The progress within these groups will indicate technology maturity, leading to the development of “plug-and-play” technologies that facilitate seamless integration and adoption within the industry.
The standard development process is a fundamental and unwavering aspect of successfully establishing a post-quantum cryptography market and its eventual integration into Information and Communication Technology (ICT). Certain industries, particularly those with long product life spans (exceeding 10 years), have proactively engaged with and strategized around Post-quantum cryptography developments. A prime example of this proactive stance is found in the automotive industry, where modern cars are increasingly reliant on software and connectivity. Therefore, current product development must incorporate quantum safeguards to prepare for the future. This, in turn, impacts the supply chain, particularly semiconductor manufacturers, who need to ensure that their chipsets can accommodate
Post-quantum cryptography readiness.
Similarly, highly regulated and sensitive sectors like financial services, defense, and telecommunications face quantum security risks. Even though commercially viable attack-capable quantum computers are not yet available, threat actors actively steal encrypted data to decrypt it once such computers become accessible. In essence, the risks are already immediate. The level of readiness in these sectors varies significantly and can be influenced by the existence of government policies in their respective regions.
The disparity in approaches can be attributed, in large part, to the complexity of Post-quantum cryptography-based key exchange and the challenges in making these schemes practical for a wide array of applications. There is no one-size-fits-all solution, which underscores the importance of industry consortia efforts.
The Need for a Unified Approach to Standards
The situation is further compounded by multiple standards based on various algorithms. This marks a significant shift in the cryptographic landscape, which, over the past decade, has only had to contend with one new cryptographic algorithm – elliptic curve cryptography (ECC). While a more streamlined approach with fewer standards would benefit the migration process, the need for distinct algorithms based on specific applications and intended use cases cannot be overlooked.
Another challenge arises in the realm of public awareness, which, on the whole, has remained relatively low-key beyond the confines of the security industry. Given that quantum computing is still largely theoretical, Post-Quantum Cryptography is not a prominent topic for many. Despite the evident risks, its critical significance has not been effectively communicated to generate widespread interest beyond a select, niche audience.
Finally, many are cautious, waiting until finalized standards and readily available commercial solutions emerge. There is a prevailing apprehension about the potential cost of prematurely implementing post-quantum cryptography. What if one of the standards is compromised within the next year? What if attack-capable quantum computers do not materialize for another two decades? Is the allocation of resources justifiable in such circumstances? Additionally, other immediate security concerns, such as ransomware and supply chain attacks, may warrant a more prudent allocation of security budgets.
The Time to Think About Post-quantum cryptography Is Now
At the worst end of the spectrum, some may adopt a passive approach, deferring Post-quantum cryptography considerations until attack-capable quantum computers become commercially feasible, which would be misguided.
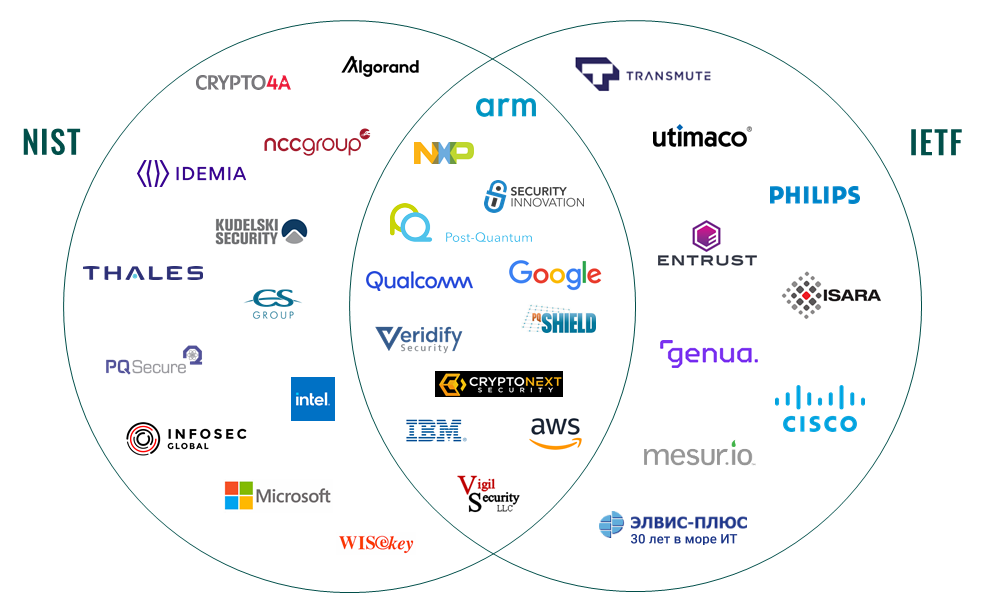
Nevertheless, the ongoing progress led by NIST and the IETF underscores that Post-Quantum Cryptography is far from being a mere abstract concept that can be easily dismissed. These collective endeavors have involved some of the world’s most prominent and influential technology and security companies over several years (as depicted below).
Incorporating Post-quantum cryptography will penetrate their product portfolios and solutions, promoting a broader understanding and awareness of Post-quantum cryptography. Although still in its early stages, this is a protracted and intricate journey, from establishing standards to its widespread integration, even after five years of development.
ContactContact
Stay in touch with Us

